What is BurpSuite?
Burp Suite is a Java based Web Penetration Testing framework. It has become an industry standard suite of tools used by information security professionals. Burp Suite helps you identify vulnerabilities and verify attack vectors that are affecting web applications. Because of its popularity and breadth as well as depth of features, we have created this useful page as a collection of Burp Suite knowledge and information.
In its simplest form, Burp Suite can be classified as an Interception Proxy. While browsing their target application, a penetration tester can configure their internet browser to route traffic through the Burp Suite proxy server. Burp Suite then acts as a (sort of) Man In The Middle by capturing and analyzing each request to and from the target web application so that they can be analyzed.
Everyone has their favorite security tools, but when it comes to mobile and web applications I've always found myself looking BurpSuite . It always seems to have everything I need and for folks just getting started with web application testing it can be a challenge putting all of the pieces together. I'm just going to go through the installation to paint a good picture of how to get it up quickly.
BurpSuite is freely available with everything you need to get started and when you're ready to cut the leash, the professional version has some handy tools that can make the whole process a little bit easier. I'll also go through how to install FoxyProxy which makes it much easier to change your proxy setup, but we'll get into that a little later.
Requirements and assumptions:
Mozilla Firefox 3.1 or Later Knowledge of Firefox Add-ons and installation The Java Runtime Environment installed
Download BurpSuite from http://portswigger.net/burp/download.htmland make a note of where you save it.
on for Firefox from https://addons.mozilla.org/en-US/firefox/addon/foxyproxy-standard/
If this is your first time running the JAR file, it may take a minute or two to load, so be patient and wait.
Video for setup and installation.
You need to install compatible version of java , So that you can run BurpSuite.
More information
- Nsa Hack Tools Download
- Pentest Tools For Windows
- Hack Apps
- Hacking Tools For Windows 7
- Hacker Tools List
- Hacking Tools Mac
- Pentest Tools Online
- Pentest Tools For Android
- Pentest Tools Linux
- Pentest Tools Tcp Port Scanner
- Hacker Tools For Pc
- Hack Website Online Tool
- Hacker Tools
- Hack Website Online Tool
- Hacker Hardware Tools
- Pentest Tools Open Source
- Hacking Apps
- Pentest Tools Port Scanner
- Hacking Tools Mac
- Hack Tools For Windows
- Hack Apps
- Hacker Tools For Mac
- Pentest Box Tools Download
- Hacking Tools For Windows
- Hak5 Tools
- Hak5 Tools
- Hacking Tools Usb
- Physical Pentest Tools
- Pentest Recon Tools
- Computer Hacker
- Hacker Techniques Tools And Incident Handling
- Hacking Tools Pc
- Hacking Tools Github
- New Hack Tools
- Pentest Tools
- Ethical Hacker Tools
- Pentest Tools Website
- What Are Hacking Tools
- Termux Hacking Tools 2019
- Hack Tool Apk No Root
- Android Hack Tools Github
- Hack Tools Online
- Hack Tools 2019
- Hacking Tools For Kali Linux
- Hacking Tools Mac
- Hacker Tools Online
- Hacker Tools Linux
- Hacker Tools Windows
- Blackhat Hacker Tools
- Usb Pentest Tools
- New Hacker Tools
- New Hacker Tools
- Hacking Tools For Windows 7
- Hack Tools
- Hacker Tools List
- Pentest Tools For Android
- Hacking Tools 2020
- Hacker Tools For Pc
- Hacking Tools For Mac
- Hacking Tools Online
- Hacker Techniques Tools And Incident Handling
- Pentest Tools Download
- How To Install Pentest Tools In Ubuntu
- Wifi Hacker Tools For Windows
- Pentest Tools For Windows
- Tools For Hacker
- How To Make Hacking Tools
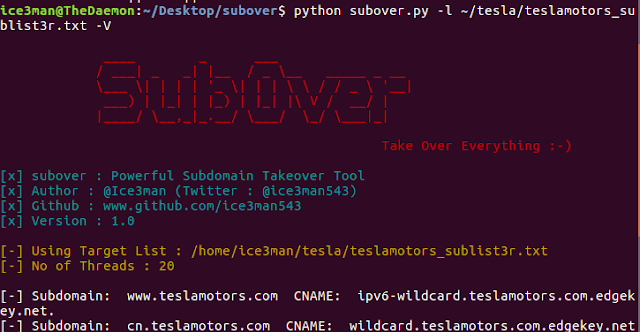
- Pentest Tools Subdomain
- What Is Hacking Tools
- Nsa Hack Tools Download
- Computer Hacker
- Hacking Tools Windows
- Pentest Tools For Mac
- Hack Tools Pc
- Hacking App




.jpg)