- SecTools.Org: List of 75 security tools based on a 2003 vote by hackers.
- The Hacker News: The Hacker News — most trusted and widely-acknowledged online cyber security news magazine with in-depth technical coverage for cybersecurity.
- Hakin9: E-magazine offering in-depth looks at both attack and defense techniques and concentrates on difficult technical issues.
- KitPloit: Leading source of Security Tools, Hacking Tools, CyberSecurity and Network Security.
- Exploit DB: An archive of exploits and vulnerable software by Offensive Security. The site collects exploits from submissions and mailing lists and concentrates them in a single database.
- Hacked Gadgets: A resource for DIY project documentation as well as general gadget and technology news.
- Packet Storm: Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers.
- Phrack Magazine: Digital hacking magazine.
- HackRead: HackRead is a News Platform that centers on InfoSec, Cyber Crime, Privacy, Surveillance, and Hacking News with full-scale reviews on Social Media Platforms.
- Metasploit: Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the worlds best penetration testing software now.
Tuesday, June 30, 2020
10 Useful Websites for Hackers
Thursday, June 11, 2020
Resolución De ExpedientesX De Código
Hoy me he topado con algo bastante gracioso que puede liarte unos minutos:
python
>>> import re
>>> a='owjf oasijf aw0oifj osfij 4.4.4.4 oasidjfowefij 192.168.1.1'
ok, pues ahora copy-pasteais cada una de estas:
re.findall('[0-9]̣̣',a)
re.findall('[0-9]',a)
Son exactamente iguales, pero si paseteais una da resultados diferente a si pasteais la otra :)
Pasteamos la primera:
>>> re.findall('[0-9]̣̣',a)
[]
Pasteamos la segunda:
>>> re.findall('[0-9]',a)
['0', '4', '4', '4', '4', '1', '9', '2', '1', '6', '8', '1', '1']
o_O, he repasado caracter a caracter y son visualmente iguales, si mirais en un editor hexa vereis que realmente no lo son, lógicamente no se trata de un expedienteX.
La cuestion es que según la fuente que tengais, debajo de la comilla o debajo del ] hay un punto microscópico :)
Esto es como cuando me emparanoie de que gmail cuando llevas un rato escribiendo un email y se hace auto-save, aparece una especie de acento raro en la pantalla :)
En estos casos, la metodología tipica de copypastear un trozo de la primera sentencia con el resto de la segunda sentencia, te lleva a los 2 caracteres que varían, pero no aprecias (segun la fuente que tengas) la diferéncia.
6572 662e 6e69 6164 6c6c 2728 305b 392d cc5d cca3 27a3 612c 0a29
6572 662e 6e69 6164 6c6c 2728 305b 392d 275d 612c 0a29
Son dígitos unicode, sabe Dios de que pais, y sabe Dios también como los escribí con mi teclado,
se me ocurren bromas de código fuente que se pueden hacer con esto :D, pero vamos, si tenemos metodología de reaccién ante expedientesX, sobretodo aquello de divide y vencerás dicotómico, en pocos minutos se resuelven este tipo de problemas.More articles
python
>>> import re
>>> a='owjf oasijf aw0oifj osfij 4.4.4.4 oasidjfowefij 192.168.1.1'
ok, pues ahora copy-pasteais cada una de estas:
re.findall('[0-9]̣̣',a)
re.findall('[0-9]',a)
Son exactamente iguales, pero si paseteais una da resultados diferente a si pasteais la otra :)
Pasteamos la primera:
>>> re.findall('[0-9]̣̣',a)
[]
Pasteamos la segunda:
>>> re.findall('[0-9]',a)
['0', '4', '4', '4', '4', '1', '9', '2', '1', '6', '8', '1', '1']
o_O, he repasado caracter a caracter y son visualmente iguales, si mirais en un editor hexa vereis que realmente no lo son, lógicamente no se trata de un expedienteX.
La cuestion es que según la fuente que tengais, debajo de la comilla o debajo del ] hay un punto microscópico :)
Esto es como cuando me emparanoie de que gmail cuando llevas un rato escribiendo un email y se hace auto-save, aparece una especie de acento raro en la pantalla :)
En estos casos, la metodología tipica de copypastear un trozo de la primera sentencia con el resto de la segunda sentencia, te lleva a los 2 caracteres que varían, pero no aprecias (segun la fuente que tengas) la diferéncia.
6572 662e 6e69 6164 6c6c 2728 305b 392d cc5d cca3 27a3 612c 0a29
6572 662e 6e69 6164 6c6c 2728 305b 392d 275d 612c 0a29
Son dígitos unicode, sabe Dios de que pais, y sabe Dios también como los escribí con mi teclado,
se me ocurren bromas de código fuente que se pueden hacer con esto :D, pero vamos, si tenemos metodología de reaccién ante expedientesX, sobretodo aquello de divide y vencerás dicotómico, en pocos minutos se resuelven este tipo de problemas.More articles
- Pentestmonkey Cheat Sheet
- Pentest Web Application
- Pentest Book
- Pentest Methodology
- Hacking Games Online
- Pentest Vs Ethical Hacking
- Hacking With Linux
- Basic Pentest 1 Walkthrough
- Pentest Website
- Pentest Training
- Pentest Firewall
- Hacking 3Ds
- Hacking Page
- Hacking For Dummies
- Hacking Apps
- Pentest Distro
- Hacking Page
- Pentesting And Ethical Hacking
- Pentesting
Wednesday, June 10, 2020
BurpSuite Introduction & Installation
What is BurpSuite?
Burp Suite is a Java based Web Penetration Testing framework. It has become an industry standard suite of tools used by information security professionals. Burp Suite helps you identify vulnerabilities and verify attack vectors that are affecting web applications. Because of its popularity and breadth as well as depth of features, we have created this useful page as a collection of Burp Suite knowledge and information.
In its simplest form, Burp Suite can be classified as an Interception Proxy. While browsing their target application, a penetration tester can configure their internet browser to route traffic through the Burp Suite proxy server. Burp Suite then acts as a (sort of) Man In The Middle by capturing and analyzing each request to and from the target web application so that they can be analyzed.
Everyone has their favorite security tools, but when it comes to mobile and web applications I've always found myself looking BurpSuite . It always seems to have everything I need and for folks just getting started with web application testing it can be a challenge putting all of the pieces together. I'm just going to go through the installation to paint a good picture of how to get it up quickly.
BurpSuite is freely available with everything you need to get started and when you're ready to cut the leash, the professional version has some handy tools that can make the whole process a little bit easier. I'll also go through how to install FoxyProxy which makes it much easier to change your proxy setup, but we'll get into that a little later.
Requirements and assumptions:
Mozilla Firefox 3.1 or Later Knowledge of Firefox Add-ons and installation The Java Runtime Environment installed
Download BurpSuite from http://portswigger.net/burp/download.htmland make a note of where you save it.
on for Firefox from https://addons.mozilla.org/en-US/firefox/addon/foxyproxy-standard/
If this is your first time running the JAR file, it may take a minute or two to load, so be patient and wait.
Video for setup and installation.
You need to install compatible version of java , So that you can run BurpSuite.
Related news
Tuesday, June 9, 2020
Hacking All The Cars - Part 1
A step by step lab based mini course on analyzing your car network
I wanted to learn about hacking cars. As usual I searched around the internet and didn't find any comprehensive resources on how to do this, just bits and pieces of the same info over and over which is frustrating. I am not a car hacking expert, I just like to hack stuff. This mini course will run in a fully simulated lab environment available from open garages, which means in 5 minutes from now you can follow along and hack cars without ever bricking your girlfriends car. Since you obviously wouldn't attack your own Lambo, totally use your girlfriends Prius.
Below are the topics covered in this blog series so you can decide if you want to read further:
Whats covered in this car hacking mini course:
Setting up Virtual Environments for testing
Sniffing CAN Traffic
Parsing CAN Traffic
Reverse Engineering CAN IDs
Denial of service attacks
Replaying/Injecting Traffic
Coding your own CAN Socket Tools in python
Targeted attacks against your cars components
Transitioning this to attacking a real car with hardware
The first thing we are going to do before we get into any car hacking specifics such as "WTF is CAN?", is get your lab up and running. We are going to run a simple simulated CAN Bus network which controls various features of your simulated car. Its better to learn by doing then sit here and recite a bunch of car network lingo at you and hope you remember it.
I also don't want you to buy a bunch of hardware and jack into your real car right away. Instead there are options that can get you started hacking cars RIGHT NOW by following along with this tutorial. This will also serve to take away the fear of hacking your actual car by understanding what your doing first.
Video Playlist:
Setting up your Lab:
First things first, set yourself up with an Ubuntu VMware install, and load it up. Optionally you could use a Kali Iinux VM, however, that thing drives me nuts with copy paste issues and I think Kayak was giving me install problems. So support is on you if you would like to use Kali. However, I do know Kali will work fine with OpenGarages virtual car.. So feel free to use it for that if you have it handy and want to get started right away.
Install PreReq Libraries:
Once you load this up you are going to want to install CAN utilities and pre-requisite libraries. This is really easy to do with the following Apt-get commands:
sudo apt-get update
sudo apt-get install libsdl2-dev libsdl2-image-dev can-utils
Then we are going to pull down the ICSimulator repo:
git clone https://github.com/zombieCraig/ICSim.git
Starting the simulator:
Once this is done we can startup the simulator by changing directories to the downloaded repo and running the following 2 commands, which will setup a virtual CAN interface and a simulator GUI Cluster:
Run the setup Script to get the vcan0 interface up:
root@kali:~/ICSim# ./setup_vcan.sh
root@kali:~/ICSim# ./icsim vcan0
On a new terminal tab we will open up our simulators controller with the following command,
root@kali:~/ICSim#./controls vcan0
Note: that the controller must be the in-focus GUI screen to send keyboard commands to the simulator.
How to Use the Simulator:
The simulator has a speedometer with Right and Left turn signals, doors etc. Below are the list of commands to control the simulator when the Control panel is in focus. Give them each a try and note the changes to the simulator.
Up and Down keys control the gauges clusters speedometer
Left and Right keys Control the Blinkers
Right Shift + X, A or B open doors
Left Shift + X, A or be Close doors
Try a few of the above commands for example Right Shift +X and you will see the interface change like so, notice the open door graphic:
Awesome, thanks to OpenGarages you now you have your very own car to hack
Notice in the setup commands above we used a VCan0 interface. Run Ifconfig and you will now see that you indeed have a new network interface that speaks to the CAN network over VCan0.
ficti0n@ubuntu:~/Desktop/ICSim$ ifconfig vcan0
vcan0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00
UP RUNNING NOARP MTU:16 Metric:1
RX packets:558904 errors:0 dropped:0 overruns:0 frame:0
TX packets:558904 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1
RX bytes:3663935 (3.6 MB) TX bytes:3663935 (3.6 MB)
Car networks run on a variety of protocols most prevalent being CAN. You can think of a CAN Bus like an old school networking hub where everyone can see everyone elses traffic. This is true to some extent although you may not see all of the cars traffic if its not connected to that particular bus your plugged into. You can think of CAN traffic kind of like UDP in that its send and forget, the main difference being parts of the CAN bus network don't actually have addresses and everything runs off arbitration IDs and priorities. Thats enough background to get you doing rather then reading.
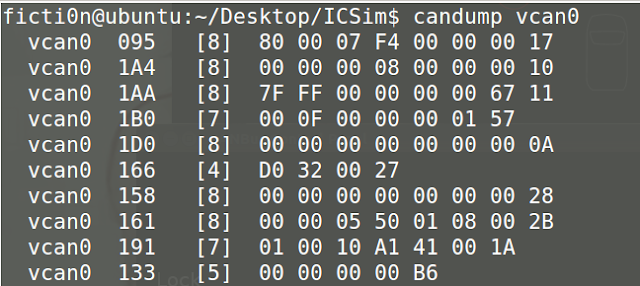
With a little knowledge out of the way lets check if we can see our CAN traffic from our virtual car via the CanDump utility, which you installed as part of CanUtils package above. Using the following command on the vcan0 interface our simulator uses you can view a stream of traffic:
With a little knowledge out of the way lets check if we can see our CAN traffic from our virtual car via the CanDump utility, which you installed as part of CanUtils package above. Using the following command on the vcan0 interface our simulator uses you can view a stream of traffic:
ficti0n@ubuntu:~/Desktop/ICSim$ candump vcan0
Above we can see a bunch of CAN frames, and if we perform actions on the vehicle we will see changes to data values in the CanDump output. However this may happen very fast, and we may not be able to see if for example we unlocked our simulators door. This is because things are changing constantly in the cars IDLE state. One single value changing may not stand out enough for us to take notice or may scroll so fast we cant see it.
Capture and Replay CAN Actions:
One option would be to perform an action and replay it, we should see the actions happen again in the replay if the traffic for the action we recorded is on the same bus network our device is plugged into. There are loads of networks within a car and its not guaranteed our network tap for example an OBD2 port plugin is connected to the same network as door we opened. Or the door may not be connected to the network at all depending on your car and its age or how its configured.
Replaying dumps with CanPlayer:
Another useful tool included with CanUtils package is CanPlayer for replaying traffic. If the functionality we are trying to capture is on the same Bus as the adaptor plugged into the car, or in this case our Virtual CAN interface, we can use CanDump to save traffic to a file. We then use CanPlayer to replay the traffic on the network. For example lets run CanDump and open a door and then replay the functionality with CanPlayer.
Lab 1 Steps:
- Run CanDump
- Right Shift + X to open a door
- Cancel CanDump (ctrl+c)
- Left Shift + X to close the door
- Run can player with the saved dump and it will replay the traffic and open the door
Recording the door opening: (-l for logging)
ficti0n@ubuntu:~/Desktop/ICSim$ candump -l vcan0
Replaying the CanDump file: (use the file your can dump created)
ficti0n@ubuntu:~/Desktop/ICSim$ canplayer -I candump-2018-04-06_154441.log
Nice, so if all went well you should see that your door is now open again. If this did not happen when attacking a real car, just try to replay it again. CAN networks are not like TCP/IP, they are more like UDP in that you send out your request and its not expecting a response. So if it gets lost then it gets lost and you have to resend. Perhaps something with higher priority on the network was sending at the time of your replay and your traffic was overshadowed by it.
Interacting with the Can Bus and Reversing Traffic:
So thats cool, but what about actually understanding what is going on with this traffic, CanDump is not very useful for this, is scrolls by to quickly for us to learn much from. Instead we can use CanSniffer with colorized output to show us the bytes within packets that change. Below is an example of CanSniffer Traffic:
To startup can sniffer run the following:
ficti0n@ubuntu:~/Desktop/ICSim$ cansniffer -c vcan0
You will see 3 fields, Time, ID and Data. Its pretty easy to figure out what these are based on thier name. The most important part for our usage in this blog are the ID and the Data fields.
The ID field is the frame ID which is loosely associated with the device on the network which is effected by the frame being sent. The ID to also determines the priority of the frame on the network. The lower the number of the CAN-ID the higher priority it has on the network and more likely it will be handled first. The data field is the data being sent to change some parameter like unlocking a door or updating output. You will notice that some of the bytes are highlighted RED. The values in red are the values that are changing during the idle state you are currently in.
The ID field is the frame ID which is loosely associated with the device on the network which is effected by the frame being sent. The ID to also determines the priority of the frame on the network. The lower the number of the CAN-ID the higher priority it has on the network and more likely it will be handled first. The data field is the data being sent to change some parameter like unlocking a door or updating output. You will notice that some of the bytes are highlighted RED. The values in red are the values that are changing during the idle state you are currently in.
Determine which ID and Byte controls the throttle:
So with the terminal sniffing window open put the simulator and the controller into the foreground, with the controller being the window you have clicked and selected. Pay attention to the CanSniffer output while hitting the UP ARROW and look for a value that was white but is now Red and increasing in value as the throttle goes up. This might take you a few minutes of paying attention to whats going on to see.
The following 2 pictures show ID 244 in the IDLE state followed by pressing the up button to increase the speed. You will notice a byte has turned red and is increasing in value through a range of HEX values 0-F. It will continue to enumerate through values till it reaches its max speed.
The byte in ID 244 which is changing is the value while the throttle is engaged, so 244 associated in some way with the increasing speed. The throttle speed is a good value to start with as it keeps increasing its value when pressed making it easier to spot while viewing the CanSniffer output.
Singling out Values with Filters:
If you would like to single out the throttle value then click the terminal window and press -000000 followed by the Enter key which will clear out all of the values scrolling. Then press +244 followed by the Enter key which will add back the throttle ID. You can now click the controller again and increase the speed with your Up arrow button without all the noise clouding your view. You will instead as shown below only have ID 244 in your output:
To get back all of the IDs again click the terminal window and input +000000 followed by the Enter key. Now you should see all of the output as before. Essentially 000000 means include everything. But when you put a minus in front of it then it negates everything and clears your terminal window filtering out all values.
Determine Blinker ID:
Now lets figure out another ID for the blinkers. If you hit the left or right arrow with the controls window selected you will notice a whole new ID appears in the list, ID 188 shown in the picture below which is associated with the blinker.
This ID was not listed before as it was not in use within the data output until you pressed the blinker control. Lets single this value out by pressing -000000 followed by +188. Just like in the throttle example your terminal should only show ID 188, initially it will show with 00 byte values.
As you press the left and the right blinker you will see the first Byte change from 00 to 01 or 02. If neither is pressed as in the screenshot above it will be 00. Its kind of hard to have the controller in focus and get a screenshot at the same time but the ID will remain visible as 00 until it times out and disappears from the list when not active. However with it filtered out as above you can get a better view of things and it wont disappear.
Time for YOU to do some Protocol Reversing:
This lab will give you a good idea how to reverse all of the functionality of the car and associate each action with the proper ID and BYTE. This way you can create a map of intended functionality changes you wish to make. Above we have done a few walk throughs with you on how to determine which byte and ID is associated with an action. Now its time to map everything out yourself with all the remaining functionality before moving on to attacking individual components.
Lab Work Suggestion:
- Take out a piece of paper and a pencil
- Try unlocking and locking doors and write down the ID which controls this action (remember your filters)
- Try unlocking each door and write down the BYTES needed for each door to open
- Try locking each doors and what Bytes change and what are their values, write them down
- Do the same thing for the blinkers left and right (Might be different then what I did above)
- What ID is the speedometer using? What byte changes the speed?
Attacking Functionality Directly:
With all of the functionality mapped out we can now try to target various devices in the network directly without interacting with the controllers GUI. Maybe we broke into the car via cellular OnStar connection or the center console units BLE connection which was connected to the CAN network in some way.
After an exploit we have direct access to the CAN network and we would like to perform actions. Or maybe you have installed a wireless device into an OBD2 port under the dashboard you have remote access to the automobile.
After an exploit we have direct access to the CAN network and we would like to perform actions. Or maybe you have installed a wireless device into an OBD2 port under the dashboard you have remote access to the automobile.
Using the data from the CAN network reversing lab above we can call these actions directly with the proper CAN-ID and Byte. Since we are remote to the target we can't just reach over and grab the steering wheel or hit the throttle we will instead send your CAN frame to make the change.
One way we can do this is via the CanSend utility. Lets take our information from our lab above and make the left turn signal flash with the following ID 188 for the turn signal by changing the first byte to 01 indicating the left signal is pressed. CanSend uses the format ID#Data. You will see this below when sending the turn signal via CanSend.
ficti0n@ubuntu:~/Desktop/ICSim$ cansend vcan0 188#01000000
You should have noticed that the left signal flashed. If not pay more attention and give it another try or make sure you used the correct ID and changed the correct byte. So lets do the same thing with the throttle and try to set the speed to something with ID 244 that we determined was the throttle.
ficti0n@ubuntu:~/Desktop/ICSim$ cansend vcan0 244#00000011F6
My guess is that nothing happened because its so fast the needle is not going to jump to that value. So instead lets try repeating this over and over again with a bash loop which simply says that while True keep sending the throttle value of 11 which equates to about 30mph:
ficti0n@ubuntu:~/Desktop/ICSim$ while true; do cansend vcan0 244#00000011F6; done
Yes thats much better, you may notice the needle jumping back and forth a bit. The reason the needle is bouncing back and forth is because the normal CAN traffic is sent telling the car its actually set to 00 in between your frames saying its 30mph. But it worked and you have now changed the speed the car sees and you have flashed the blinker without using the cars normal blinker controls. Pretty cool right?
Monitor the CAN Bus and react to it:
Another way to handle this issue is to monitor the CAN network and when it sees an ID sent it will automatically send the corresponding ID with a different value.. Lets give that a try to modify our speed output by monitoring for changes. Below we are simply running CanDump and parsing for ID 244 in the log output which is the throttle value that tells the car the speed. When a device in the car reports ID 244 and its value we will immediately resend our own value saying the speed is 30mph with the value 11. See below command and try this out.
ficti0n@ubuntu:~/Desktop/ICSim$ candump vcan0 | grep " 244 " | while read line; do cansend vcan0 244#00000011F6; done
With this running after a few seconds you will see the speed adjust to around 30MPH once it captures a legitimate CAN-ID 244 from the network traffic and sends its own value right after.
Ok cool, so now while the above command is still running click the controller window and start holding down the Up arrow with the controller in focus.. After a few seconds or so when the speed gets above 30MPH you will see the needle fighting for the real higher value and adjusting back to 30MPH as your command keeps sending its on value as a replacement to the real speed.
So thats one way of monitoring the network and reacting to what you see in a very crude manner. Maybe someone stole your car and you want to monitor for an open door and if they try to open the door it immediately locks them in.
Conclusion and whats next:
I am not an expert car hacker but I hope you enjoyed this. Thats about as far as I want to go into this subject today, in the next blog we will get into how to code python to perform actions on the CAN network to manipulate things in a similar way. With your own code you are not limited to the functionality of the tools you are provided and can do whatever you want. This is much more powerful then just using the CanUtils pre defined tools. Later on I will also get into the hardware side of things if you would like to try this on a real car where things are more complicated and things can go wrong.
Read more
Amnesia / Radiation Linux Botnet Targeting Remote Code Execution In CCTV DVR Samples
2016-08-11 CyberX Radiation IoT Cybersecurity campaign
Download

Hashes
| MD5 | SHA256 | SHA1 |
|---|---|---|
| 74bf554c4bc30d172cf1d73ac553d766 | 06d30ba7c96dcaa87ac584c59748708205e813a4dffa7568c1befa52ae5f0374 | 3c40221177383da576b11a0b3f6b35d68a9cde74 |
| 5dd9056e5ab6a92e61822b6c04afd346 | 10aa7b3863f34d340f960b89e64319186b6ffb5d2f86bf0da3f05e7dbc5d9653 | c865dd67853a24fd86ef74b05140827c1d5fd0bd |
| 2b486466f4d3e30f7b22d0bc76cb68f9 | 175fe89bbc8e44d45f4d86e0d96288e1e868524efa260ff07cb63194d04ea575 | ed62f6d1588bea33c20ababb42c02662d93d6015 |
| 3411bb2965f4c3d52c650aff04f48e52 | 1d8bc81acbba0fc56605f60f5a47743491d48dab43b97a40d4a7f6c21caca12a | 1e0281178b4a9d8dec74f50a7850867c87837435 |
| 34f915ac414e9aad2859217169f9a3aa | 2f9cd1d07c535aae41d5eed1f8851855b95b5b38fb6fe139b5f1ce43ed22df22 | d66f1e47c983a8d30ad7fd30cd08db8cd29a92b0 |
| 59e08f2ce1c3e55e2493baf36c1ad3c6 | 327f24121d25ca818cf8414c1cc704c3004ae63a65a9128e283d64be03cdd42e | 90d45b81e9a97ddcc9911122f4e8fd439ccc8fa9 |
| f4bc173bf80d922da4e755896af0db61 | 37b2b33a8e344efcaca0abe56c6163ae64026ccef65278b232a9170ada1972af | fab32f8c3ce3a837e80a1d98ada41a5bf39b01e7 |
| a253273e922ce93e2746a9791798e3fe | 3a595e7cc8e32071781e36bbbb680d8578ea307404ec07e3a78a030574da8f96 | 99cfdec405f6a9f43d58b1856fce7ca3445395d3 |
| 335e322c56278e258e4d7b5e17ad98e6 | 4313af898c5e15a68616f8c40e8c7408f39e0996a9e4cc3e22e27e7aeb2f8d54 | 504022707609a0fec9cbb21005cb0875be2a4726 |
| 93522e5f361a051f568bd1d74d901d30 | 46ea20e3cf34d1d4cdfd797632c47396d9bdc568a75d550d208b91caa7d43a9b | e7fc96b2a92888572de2539f227c9a6625449f83 |
| c86af536d87c1e5745e7d8c9f44fd25d | 4b0feb1dd459ade96297b361c69690ff69e97ca6ee5710c3dc6a030261ba69e0 | 6ef69a683913ae650634aedc40af8d595c45cb4f |
| 90c7c5e257c95047dbf52bbfbe011fd6 | 4db9924decd3e578a6b7ed7476e499f8ed792202499b360204d6f5b807f881b8 | 1c3a9be6ae9300aaad00fb87d5407ed6e84ec80b |
| 7c0528e54b086e5455ef92218ea23d03 | 5e6896b39c57d9609dc1285929b746b06e070886809692a4ac37f9e1b53b250c | 868abc912ff2fdcd733ff1da87e48e7d4c288a73 |
| 6405b42d2c7e42244ac73695bb7bfe6b | 64f03fff3ed6206337332a05ab9a84282f85a105432a3792e20711b920124707 | 173aca65181c8da84e062c803a43a404ad49302d |
| 6441157813de77d9849da5db9987d0bb | 6b2885a4f8c9d84e5dc49830abf7b1edbf1b458d8b9d2bafb680370106f93bc3 | 92dff9bdb31d3b9480d9e5f72a307715859dd094 |
| 614ea66b907314398cc14b3d2fdebe79 | 6b29b65c3886b6734df788cfc6628fbee4ce8921e3c0e8fc017e4dea2da0fd0b | c7e71c42d391f9c69375505dbf3767ba967f9103 |
| 00fe3120a666a85b84500ded1af8fb61 | 885dce73237c4d7b4d481460baffbd5694ab671197e8c285d53b551f893d6c09 | 342ed67e08d16ab982a4012fcecdca060a5da46b |
| 5477de039f7838dea20d3be1ae249fcb | 886136558ec806da5e70369ee22631bfb7fa06c27d16c987b6f6680423bc84b0 | 5b19202b45e5a58cadec8c2efa40fd924b64177d |
| 91bf10249c5d98ea6ae11f17b6ef0970 | 8f57ec9dfba8cf181a723a6ac2f5a7f50b4550dd33a34637cf0f302c43fd0243 | 682dab9ec3ff0b629cce4e16c9c74171dd2551d4 |
| fb0a7e12d2861e8512a38a6cdef3ddf0 | 9351ee0364bdbb5b2ff7825699e1b1ee319b600ea0726fd9bb56d0bd6c6670cb | c077c490bb22df9886475dc5bedfc6c032061024 |
| 9b7f5a1228fa66cbd35e75fb774fdc8e | 9c7a5239601a361b67b1aa3f19b462fd894402846f635550a1d63bee75eab0a2 | ae89bc6c5cc1818b3136a40961462327c3dececc |
| 5b97d54dc5001eb7cf238292405070a6 | a010bf82e2c32cba896e04ec8dbff58e32eee9391f6986ab22c612165dad36a0 | 96d2194f5f3927de75605f6ca6110fe683383a01 |
| 642f523bb46c2e901416047dca1c5d4e | ad65c9937a376d9a53168e197d142eb27f04409432c387920c2ecfd7a0b941c8 | bbf667213a446bc9bc4a5a2e54e7391752e3a9b8 |
| c617655312c573ecb01d292b320fff2e | aeb480cf01696b7563580b77605558f9474c34d323b05e5e47bf43ff16b67d6a | de102a6f35e08f18aa0c58358f5b22871eb0a45f |
| c8835a3d385162ae02bd4cb6c5ebac87 | b113ec41cc2fd9be9ac712410b9fd3854d7d5ad2dcaac33af2701102382d5815 | 831eb9cf0dcd57a879c04830e54a3b85fe5d6229 |
| 1497740fa8920e4af6aa981a5b405937 | b13014435108b34bb7cbcef75c4ef00429b440a2adf22976c31a1645af531252 | 8d6b90f0b88b1ad5dcc87d377e6a82dc6ac64211 |
| 5e925e315ff7a69c2f2cf1556423d5af | b3d0d0e2144bd1ddd27843ef65a2fce382f6d590a8fee286fda49f8074711545 | 64fe900b3a2b030c28211404afa45703c6869dea |
| 951ec487fb3fece58234677d7fe3e4dc | bdefa773e3f09cdc409f03a09a3982f917a0cc656b306f0ece3dd1a2564a8772 | 0b03d9471522590530dd90ad30b2d235ec98b578 |
| 3e84998197fc25cbac57870e3cdeb2de | c03b403d5de9778a2ec5949d869281f13976c2fc5b071e0f5f54277680c80902 | 0b9eb6d931dc6b226a913e89bb422f58228de0d0 |
| c3a73d24df62057e299b6af183889e6b | cb2382b818993ef6b8c738618cc74a39ecab243302e13fdddb02943d5ba79483 | 6a683ef6f7653e5ee64969cbbbe4403601ae9ded |
| d428f50a0f8cd57b0d8fe818ace6af20 | ce61dcfc3419ddef25e61b6d30da643a1213aa725d579221f7c2edef40ca2db3 | 9bd832256b94e43546dfb77532f6d70fcd1ce874 |
| e1d6d4564b35bb19d2b85ca620d7b8f2 | d0bda184dfa31018fe999dfd9e1f99ca0ef502296c2cccf454dde30e5d3a9df9 | c1af00d3263893b5d23dbf38015fe3c6a92cefaf |
| e9502ae7b0048b9ea25dd7537818904c | e7d6b3e1fba8cdf2f490031e8eb24cd515a30808cdd4aa15c2a41aa0016f8082 | 0e080ac0130ab3f7265df01b8397e4abd13c38cb |
| 8eb34e1fb7dd9d9f0e1fef2803812759 | eb54dc959b3cc03fbd285cef9300c3cd2b7fe86b4adeb5ca7b098f90abb55b8a | 5310a99f0f8c92bfa2f8da87e60c645f2cae305a |
| ca0fc25ce066498031dc4ca3f72de4b8 | f23fecbb7386a2aa096819d857a48b853095a86c011d454da1fb8e862f2b4583 | 7f4d97eea294fc567b058b09cc915be56c2a80e1 |
| 5a2fcfff8d6aab9a0abe9ca97f6093ed | f6af2fa4f987df773d37d9bb44841a720817ce3817dbf1e983650b5af9295a16 | f4ddf49fbf23edb23f50be62637a4a688e352057 |
| ed98e8fa385b39ca274e0de17b1007e6 | f7a737cb73802d54f7758afe4f9d0a7d2ea7fda4240904c0a79abae732605729 | a69d4c2b88bfe3a06245f8fbfb8abe5e9a894cec |
| 320db5f1230fcfe0672c8515eb9ddcfc | f7cf1e0d7756d1874630d0d697c3b0f3df0632500cff1845b6308b11059deb07 | 8d40dbf34a02dd43a81e5cdc58a0b11bfa9f5663 |
| 18d6af9211d0477f9251cf9524f898f3 | f97848514b63e9d655a5d554e62f9e102eb477c5767638eeec9efd5c6ad443d8 | b0e76be186fd609d5a8a33d59d16ffa3bdab1573 |
Sunday, June 7, 2020
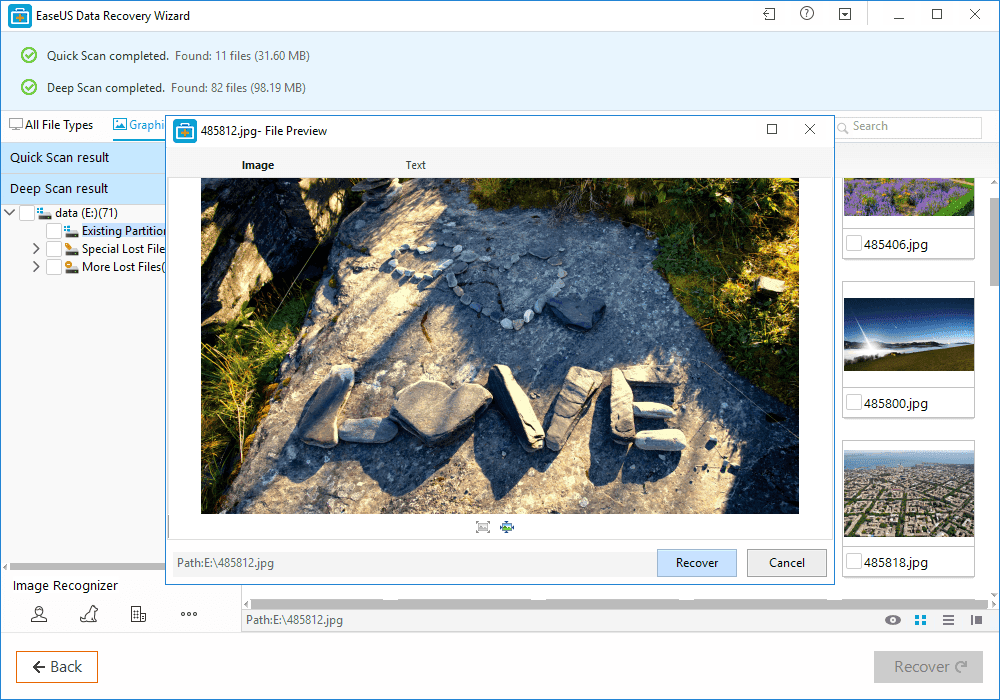
How To Recover Files That Are Deleted From Recycle Bin
How To Recover Files That Are Deleted From Recycle Bin
How To Recover Files That Are Deleted From Recycle Bin
Well, Windows users have a bad habit of removing files from recycle bin. Deleting useless files from Recycle Bin helps a user to save some storage space which can improve the speed of a computer. However, Windows users do that more frequently and later regret. Actually, Recycle Bin is a place from where we can get back our deleted files and folders.
Sometimes, we accidentally delete our important files and folders and due to some reason we lose them from Recycle bin too! At that time, we search for recovery methods. Well, there are many methods available over the web which can help you to recover deleted files from computer, but, when it comes to reliability, nothing can beat EaseUS.
What Is EaseUS Data Recovery Wizard?
EaseUS is one of the leading software providers which is known for its data recovery programme. EaseUS offers some free data recovery software that can help you to recover deleted, formatted or lost data from PC, laptop or removable device easily and quickly.
One of the best thing about EaseUS is that it provides tools for recycle bin recovery which can help you to get back files that you have deleted from the Recycle bin itself. EaseUS Data Recovery Wizard free can easily recover lost files, pictures, documents, videos and more from deleting, formatting, partition loss, OS crash, virus attack and other data loss cases.
How To Recover Deleted Files?
If you are struggling to get back your lost data files, then here is an easy data recovery method which will help you to get back deleted files on your computer. Below, we are going to share a mini guide on how to use EaseUS Recycle Bin Recovery to get back your deleted data.
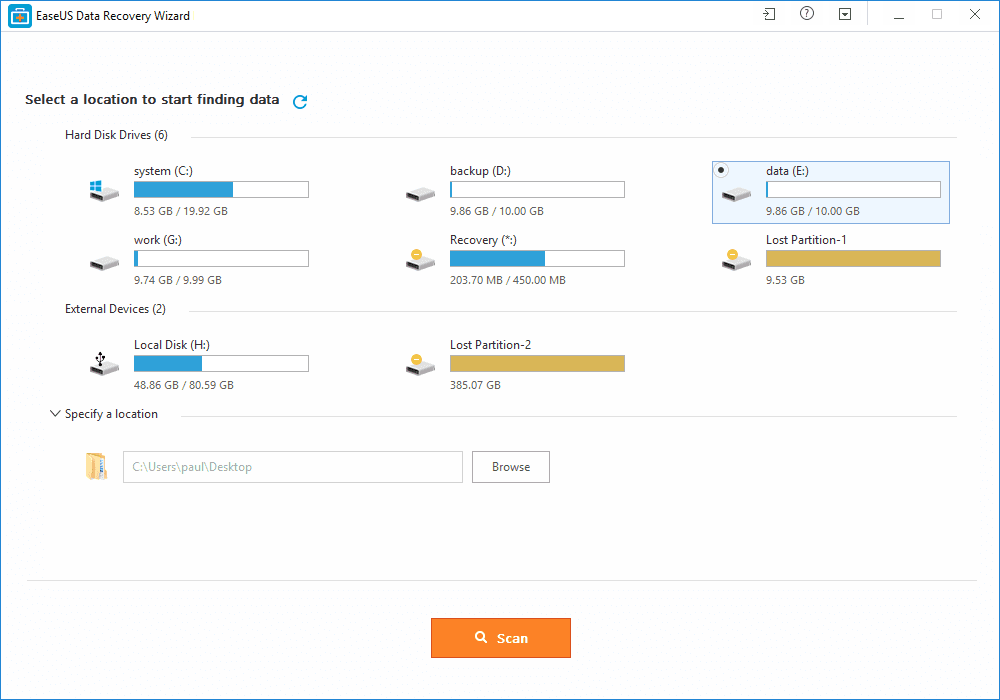
Step 1. First of all, you need to download and install EaseUS Data Recovery Wizard on your Windows computer and then launch it normally. You need to select the location where you want to scan and then click on 'Scan'
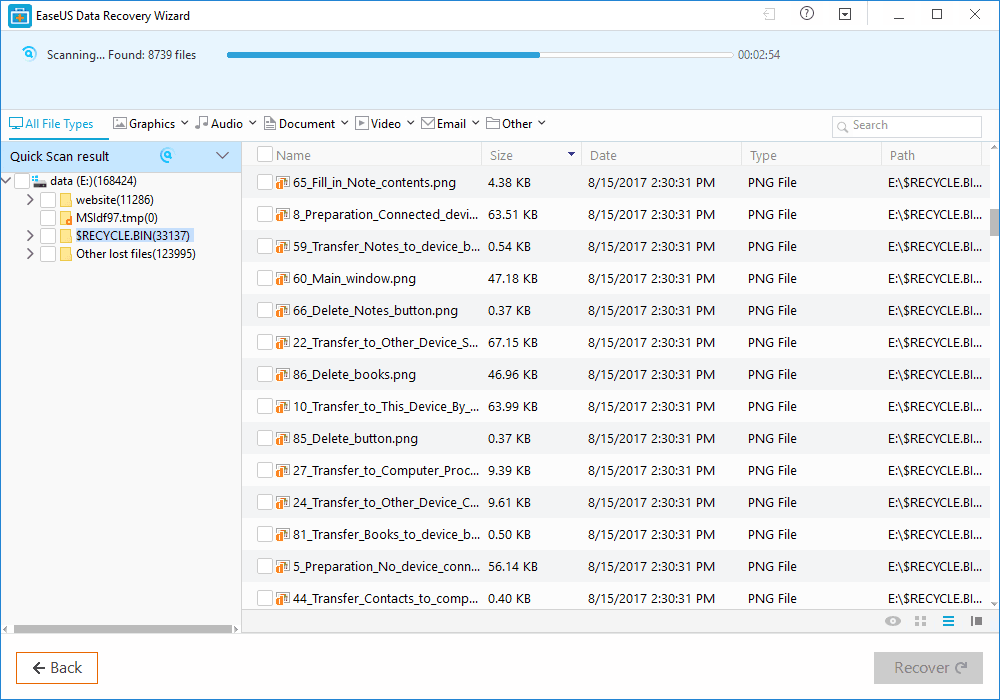
Step 2. Now, wait for few minutes until the tool finishes scanning your drive. The tool search for files that got deleted or cleaned from the Recycle Bin.
Step 3. Now it will show you files that you can recover. Here you need to click on the file which you want to recover and click on 'Recover'
That's it, you are done! This is how you can use EaseUS data recovery to get back your deleted files on your computer.
Benefits of EaseUS Data Recovery
Well, the data recovery tool provided by EaseUS comes with many benefits. It can not only recover accidentally deleted files, but it can also recover data in case of Virus Attacks, Hard Disk Damage, OS Crash etc.
You can also use this awesome data recovery wizard to recover deleted files from External Disk, USB Drive, Camcorder, Mobile Devices, Zip Drive, iPod, Music Player and more.
Overall, this is one of the best data recovery tools you can have on your Windows computer. EaseUS Data Recovery also has a free version with restricted features. Overall, this is a stress-free solution to get back your deleted files
Related posts
Subscribe to:
Posts (Atom)














.jpg)